Building a Microsoft Sentinel Data Use Case
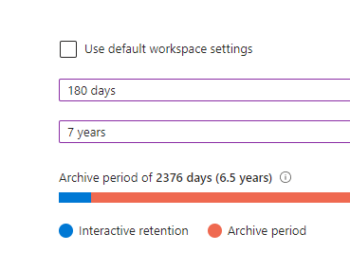
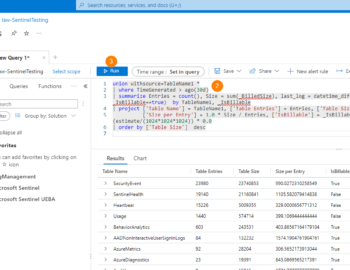
Join me this week to gain an in-depth understanding on how to clearly define what data to retain. Data retention is not just a regulatory box to tick; it’s the backbone of a robust security posture. In the realm of Microsoft Sentinel, understanding how to manage your data retention is key to leveraging the full potential of your SIEM system. From cost management to compliance, the way you handle data can make or break your security operations.