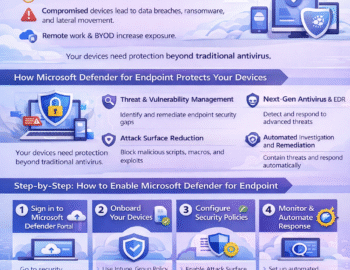
You will quickly discover that endpoints are the frontline of modern cyber defense — and the first targets for attackers. Laptops, desktops, servers, and mobile devices sit at the intersection of users, data, and the cloud, making them prime entry points for ransomware, credential theft, and lateral movement.
This article explains how Microsoft Defender for Endpoint (MDE) transforms endpoint security from a reactive antivirus solution into a proactive, intelligent, and automated threat protection platform. You will learn how to onboard devices, configure Attack Surface Reduction (ASR) rules and Network Protection, monitor alerts and incidents, and leverage Automated Investigation and Response (AIR) to stop attacks before they escalate.